
Context: in the era of virtualization, securing application will play a crucial role while deploying product in shared, dedicated or organization tenancy considering data driven nature in the era of IOT and M2M communication
following are the main pillars of securing product in the context of industry architecture for both Enterprise and solution architecture bucket.

Confidentiality: protect information and systems from unauthorised access
Integrity: protect information and systems from unauthorized modification
Availability: Ensure the system and information are available for authorized user when needed
What space: Securing product in the context of organization specific Enterprise architecture guideline that includes system, data and deployment environment including network security.
How Space: viewpoint
- Enterprise Architect and Organization security policy Viewpoint
- Solution Architect Viewpoint
- DevOps team viewpoint
Enterprise Architect and Organization security policy Viewpoint
Control frameworks can be used to guide security design with organization architecture, following are the popular control frameworks used by the organization.
- COBIT5
- ISO 27001
Overview of COBIT5 Framework
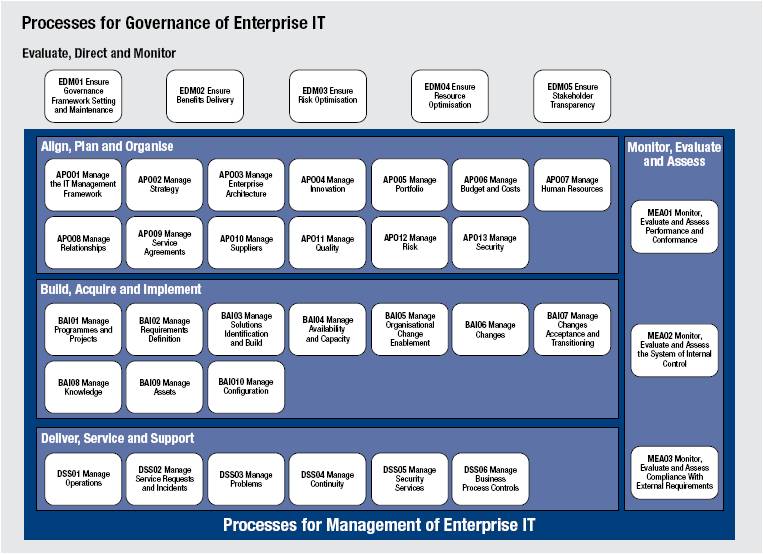
COBIT 5 is based on five principles that are essential for the effective management and governance of enterprise IT:
- Principle 1: Meeting stakeholder needs
- Principle 2: Covering the enterprise end to end
- Principle 3: Applying a single integrated framework
- Principle 4: Enabling a holistic approach
- Principle 5: Separating governance from management
These five principles enable an organisation to build a holistic framework for the governance and management of IT that is built on seven ‘enablers’:
- People, policies and frameworks
- Processes
- Organisational structures
- Culture, ethics and behaviour
- Information
- Services, infrastructure and applications
- People, skills and competencies
Together, the principles and enablers allow an organisation to align its IT investments with its objectives to realise the value of those investments.
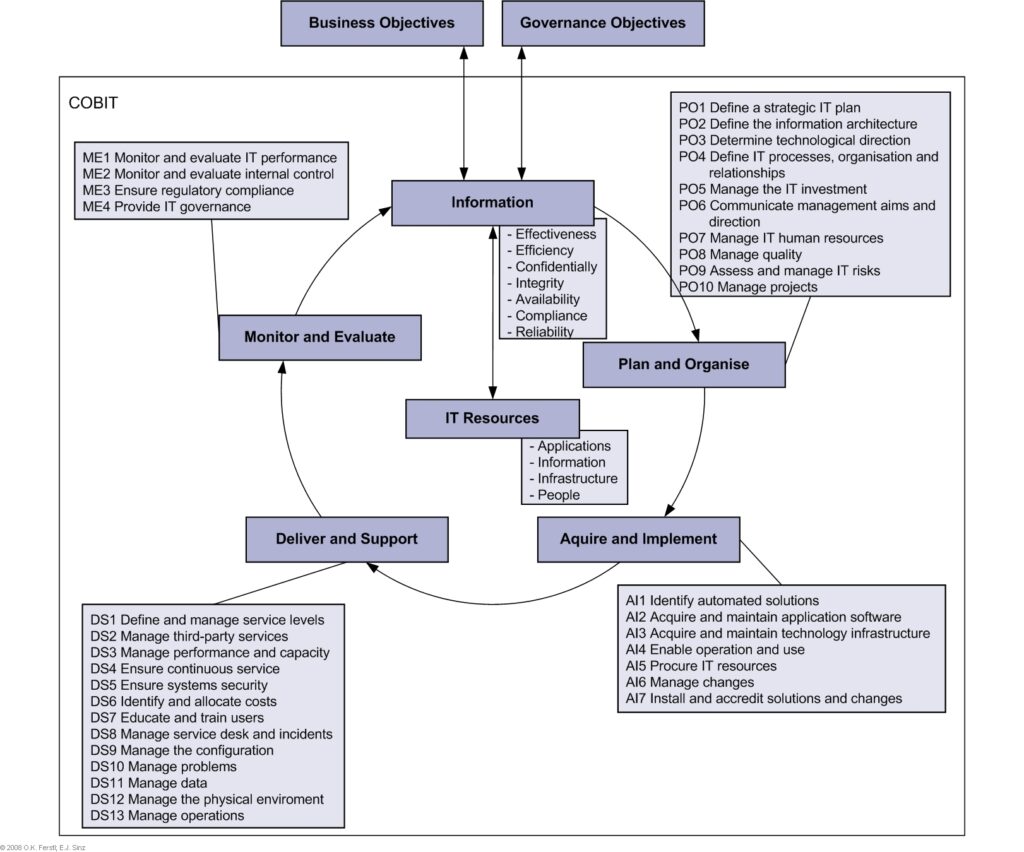
Enterprise architect to define organization specific guideline tailoring industry specific architecture with collaboration with business associates/business owner with the view of covering line of business and IT
Solution Architect Viewpoint
To working with specific solution of the organization, architect(s) shall follow Enterprise architecture guideline that includes business process(es) transformation to technical view
Following are the major areas in the context of solution architecture security
Identifying threads
- Use a structured approach to threat management
- Assets Focus: Use of asset inventory as the basis of analysis
- Threat Focus: Identify how specific threats may affect each information system
- Service focus approach: Identify the impact of various threats on a specific service
Understanding attack(s)
Use of Microsoft STRIDE model
S: Spoofing
Most security systems rely on the identification and authentication of users. Spoofing attacks consist in using another user credential without their knowledge. Typical spoofing threats target weak authentication mechanisms, for instance those using simple passwords, like a simple 4 digits number, or those using personal information that can be easily found, like date or place of birth.
T: Tampering
Only authorised users should be able to modify a system or the data it uses. If an attacker is able to tamper with it, it can have some consequences on the usage of the system itself, for instance if the attacker can add or remove some functional elements, or on the purpose of the system, for instance if important data is destroyed or modified.
R: Repudiation
Attackers often want to hide their malicious activity, to avoid being detected and blocked. They might therefore try to repudiate actions they have performed, for instance by erasing them from the logs, or by spoofing the credentials of another user.
I: Information Disclosure
Many systems contain confidential information, and attackers often aim at getting hold of it. There are numerous examples of data breaches in the recent years.
D: Denial of Service
A system is usually deployed for a particular purpose, whether it is a banking application or an integrated media management on a car. In some cases, attackers will have some interest in preventing regular users to access the system, for instance as a way to blackmail and extort money from the owner of the system (e.g., with ransomware).
E: Elevation of privilege
Once a user is identified on a system, they usually have some sort of privileges, i.e., they are authorised to perform some actions, but not necessarily all of them. An attacker might therefore try to acquire additional privileges, for instance by spoofing a user with higher privileges, or by tampering the system to change their own privileges.
Implementation of STRIDE: Vulnerability Assessment Tool
Passive Tool: Observe activity but don’t take any action
Active Tool: Interact with machine
Network Security (Enterprise Architecture and Solution Architecture common set)
Honeypot
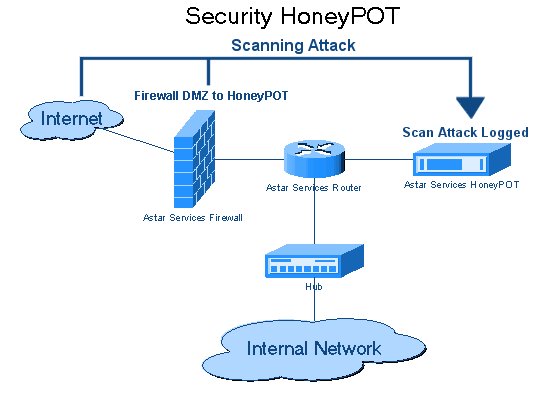
honeypot is a computer security mechanism set to detect, deflect, or, in some manner, counteract attempts at unauthorized use of information systems. Generally, a honeypot consists of data (for example, in a network site) that appears to be a legitimate part of the site that seems to contain information or a resource of value to attackers, but actually, is isolated and monitored and, enables blocking or analysing the attackers. This is similar to police sting operations, colloquially known as “baiting” a suspect.[1]
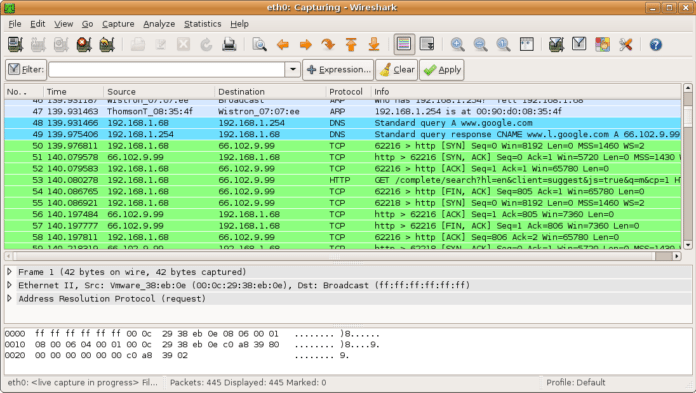
Protocol Analyzer:
protocol analyzer is a tool (hardware or software) used to capture and analyse signals and data traffic over a communication channel. Such a channel varies from a local computer bus to a satellite link, that provides a means of communication using a standard communication protocol (networked or point-to-point).
Example: wireshark: protocol analyzer
Scanning Assessment:Port Scanner
A variety of tools can be used to perform a port scan. The most commonly used tool is Nmap, which stands for Network Mapper. Nmap is a free, open source tool that offers several network mapping features, including port scanning.
Beyond Nmap, there are other tools to perform port scans — such as Metasploit and NetScanTools Pro — as well as other types of port scans that retrieve different information.
Types of port scans
Types of port scans include the following:
- Vanilla – An attempt to connect to all ports — there are 65,536.
- Strobe – An attempt to connect to only selected ports — typically, under 20.
Stealth scan. Several techniques for scanning that attempt to prevent the request for connection being logged.
- File Transfer Protocol (FTP) bounce scan. An attempt that is directed through an FTP server to disguise the cracker’s location.
- Fragmented packets. A scan performed by sending packet fragments that can get through simple packet filters in a firewall.
- UDP. A scan for open UDP ports.
- Sweep. A scan of the same port on various computers.
Why run a port scan?
A port scan’s main function is to map the ports on a given network. However, a port scanner can have a variety of reasons to run one. As mentioned before, crackers and black hat hackers use port scans to break into vulnerable networks to gain unauthorized access to sensitive information. For malicious users, a port scan is usually the prelude to an attack, a type of network reconnaissance used to identify the systems, ports and software in use that are vulnerable to attack.
However, port scans also have legitimate uses by pen testers and white hat hackers. These are people looking to identify potentially exploitable systems so that they can strengthen them against attackers. They can use port scan data in conjunction with vulnerability management tools to identify new devices or systems on a network that they need to protect or identify misconfigurations in system defences.
Vulnerability Scanner:
Nessus is a remote security scanning tool, which scans a computer and raises an alert if it discovers any vulnerabilities that malicious hackers could use to gain access to any computer you have connected to a network.
DevOps Viewpoint
To working with a specific code base, deployment and operation of the group of application to fulfill business goal or specific application following are the areas to cover with the guidance of Solution architect and leads
- Code with proper versioning tool defined by organization (viz GitHub/bitbucket etc.)
- Code commit with proper branch advice
- Code commit with use of meaningful statement
- Code coverage report (Viz static analyzer SonarQube)
- Installation and use of CI/CD tool as per organization specific policy applied (Viz Jenkins, GitLab, circle CI)
- Independent use of CI and CD pipeline with no overlapping functionality
- Use of security vault for sensitive information and credential (CyberArk)
- Integration method to use code, CI, CD and security Vault
- Use of operation specific authentication and authorization as per organization policy applied viz role of corporate or organization specific identity and access management
Conclusion:
- The aim of the document is to provide overview of security guidelines in the view of architects and DevOps -it doesn’t cover cloud security specifically
- Risk management and risk mitigation plan is out of scope of the document
- IT provides the role and security measurement for the space of enterprise, solution and DevOps bucket
Reference
https://www.ibm.com/blogs/cloud-computing/2018/01/16/drive-compliance-cloud/
https://www.itgovernance.co.uk/cobit
http://www.qualified-audit-partners.be/index.php?cont=463&lgn=3
https://www.futurelearn.com/courses/cyber-security/0/steps/19631
https://en.wikipedia.org/wiki/Honeypot_(computing)
https://securitybrief.asia/story/in-it-security-good-enough-is-no-longer-good-enough