Executive summary
Start with question – what false base station is? Is it always part of mobile eco system and how it is managed in 2G/3G/LTE or 5G, let’s deep dive into it with security context with timescale highlighting key areas of enhancement over time.
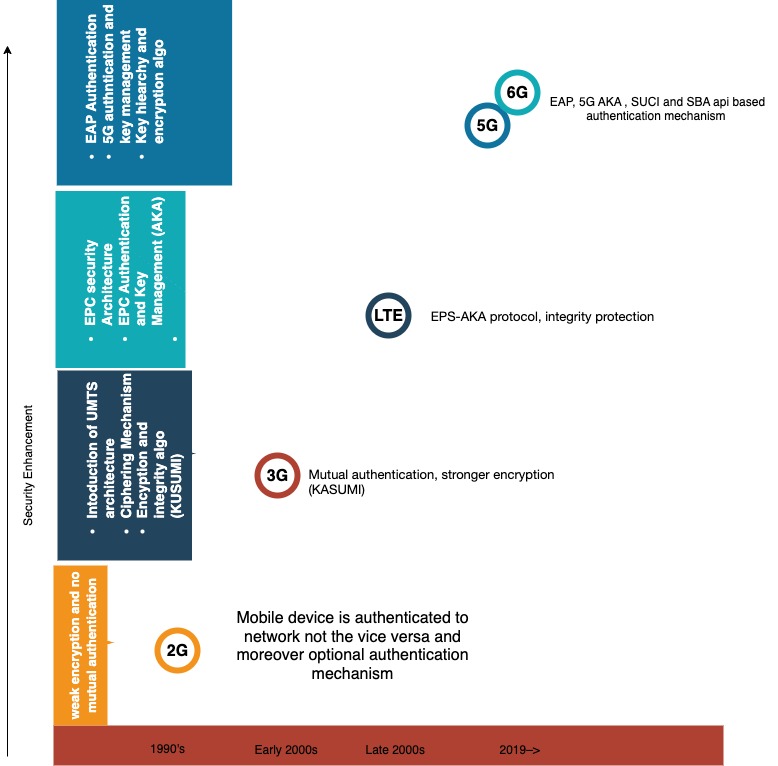
Fig 1 : Security threat and enhancement over timescale
LTE and 5G deployment
We have already discussed our previous blogs on LTE and 5G NR protocol stack including deployment architecture, we will use simplified view to understand false base station and it’s impact on NAS ans AS security context.
it includes
- LTE and 5G NR protocol stack
- 5G NR functional split including small cell deployment
- Security threats as of now in the context of false base station
- Functional split using protocol stack and implementation of RDU-DU-CU
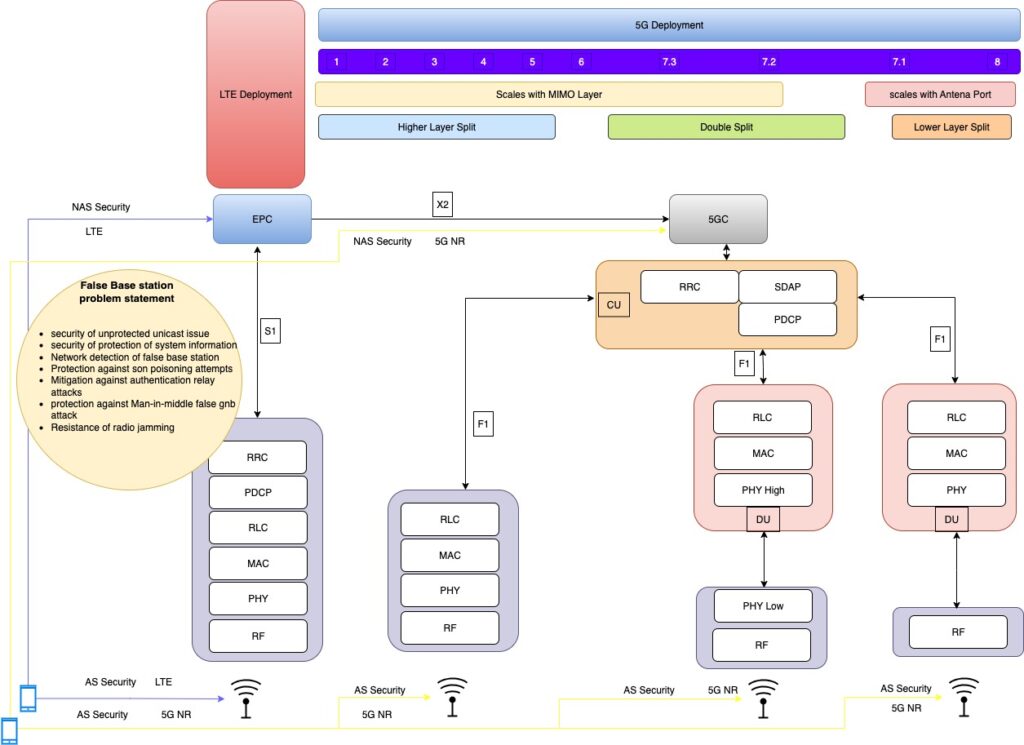
Fig 2: Functional split of 5G NR , LTE , 5G NR deployment architecture , false base station problem statement
Impact of the problem statement
#1: Security of unprotected unicast messages
- Lack of security for unprotected unicast messages could potentially have following impacts in some cases:
- DoS attack on UE.
- Limited network service. Lack of security for NAS REJECT message,
- the UE may suffer bidding down attack
#2: Security protection of system information
Lack of protection of SI could potentially have following impacts in some cases:
- DoS attack on UE Rogue services
#3: Network detection of false base stations
Undetected false base station could result in unwanted consequences without being noticed, as follow, thus depriving the network of taking corrective measures:
- DoS attack on network,
- DoS attack on UE (i.e., UE may lose incoming calls, paging messages, etc., and may not get service it requests),
- Fraud,
- Subscriber privacy attack (i.e., UE may be lured to LTE or other technology and IMSI might be revealed).
#4: Protection against SON poisoning attempts
- Poor SON implementations that do not take the possibility of SON poisoning attempts (i.e., falsified information in the measurement reports) into account could result in unwanted consequences, as follow:
- DoS attack on network
- DoS attack on UE
#5: Mitigation against the authentication relay attack
- Deception: The adversary deceives the victim into believing that the victim UE is connected to the core network.
- Location History Poisoning: The malicious UE can poison the location history of the victim UE by performing this attack successively from different tracking areas. As a result, a fugitive or criminal hiding in one location can deceive the core network into believing that the criminal has attached to the core network from a different location.
- Complete or Selective DoS: The malicious UE and the false base station can deny the victim UE’s phone- calls/SMS/data transfers completely/selectively. Consequently, the operational network is deprived of the charges for the incoming/outgoing calls and SMSs.
- Attack on SON: By relaying a geographically remote base station, an attacker may confuse the network’s self- organized network configuration, because UEs will report measurements of the false base station signal strength, or signal strength of the radio environment to the relayed base station.
#6: Resistance to radio jamming
Undetected or un-prevented radio jamming could potentially have following impacts in some cases:
- DoS attack on UE
- DoS attack on network
#7: Protection against Man-in-the-Middle false gNB attacks
- A MitM false base station may force a UE to camp on to it by passing all the message on between the UE and real base station. It may then deny the UE service, e.g. reject or drop service request, not pass on paging messages etc.
- A MitM false base station may perform a linkage attack by SUCI replay, i.e. replace a SUCI in a registration request or in an identity response by a previously captured SUCI and observe whether the UE will be authenticated and receive service.
Solutions key takeway
- Certification based solution against base station
- Protection of UE capability-information RRC message
Protection of UE capabilities transfer, RRC reject message in RRC_INACTIVE State - Integrity of RRC resume request message
- Enhanced measured report, avoiding UE connecting false base station during HO , N/W detection of nearly False base station from call statics and measurements.
- security mitigation against the authentication relay attack
- Cryptographic CRC to avoid MitM relay nodes
- Verification of authenticity of the cell
- Using symmetric algorithm with assistance of USIM and home network
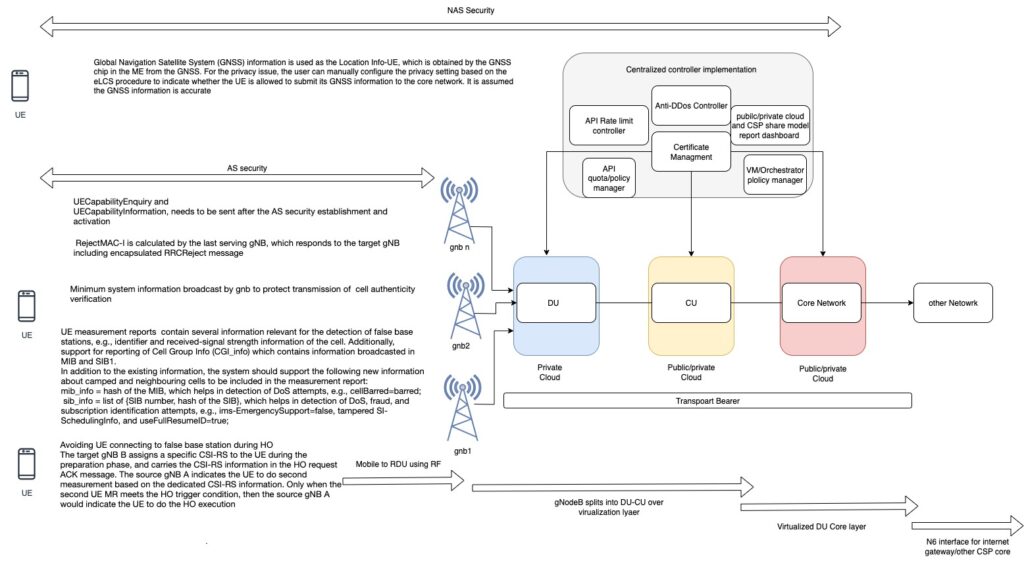
Fig 3: Key highlight of solutions within AS and NAS security including public/private and application specific security
Conclustion
Attempt to simplify on security issues form 2G to 5G – we have also covered deep dive into 5G functional split and LTE/5G deployment in the context of AS and NAS security. 5G area- associated security threat and solution approach for false base station
In the upcoming blogs we will cover
Ran security: Mobile proximity service & Satellite broadband overview.
Happy learning!